In a recent and alarming incident, popular genetic testing company 23andMe fell victim to a data breach, compromising the sensitive information of millions of its users.
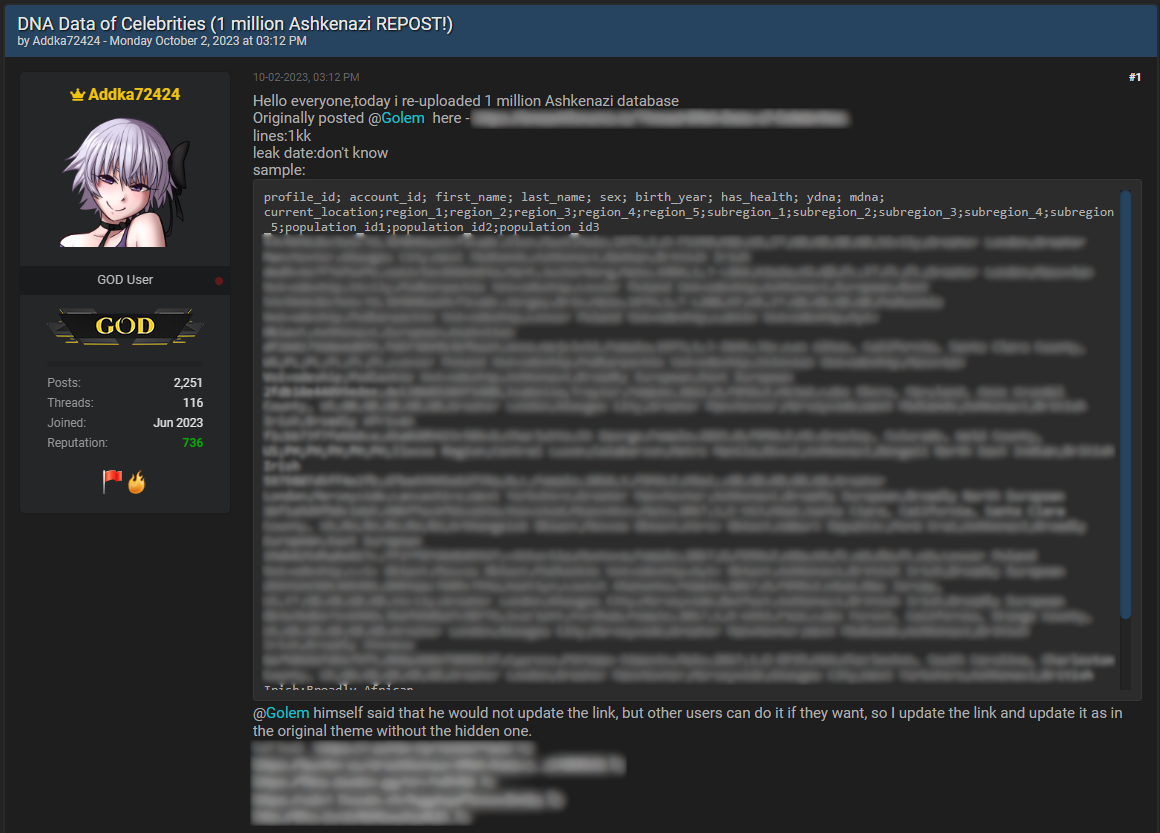
The breach came to public attention when a cybercriminal claimed to possess a substantial trove of customer data from 23andMe, boasting about the sale of "the most valuable data you'll ever see." The data reportedly included details from users who had opted into the company's "DNA Relatives" service, allowing individuals to connect with genetic relatives and delve into their family histories.
According to reports, the attackers gained access to individual accounts through credential-stuffing techniques. This method involves using login credentials leaked from other online platforms to gain unauthorized access to user accounts where individuals have reused the same usernames and passwords.
The compromised accounts were those enrolled in the "DNA Relatives" feature, inadvertently revealing unexpected privacy consequences associated with such services.
The stolen information reportedly included users' display names, profile photos, gender, birth years, geographical locations, predicted relationships to genetic matches, the percentage of DNA matches, the number of shared genetic segments, and details about genetic ancestry, such as haplogroups.
One particularly troubling aspect of the 23andMe data breach was the targeting of specific ethnic groups, notably Ashkenazi Jews. The cybercriminals behind the breach released an initial data sample containing 1 million data points exclusively about Ashkenazi Jews, indicating a deliberate focus on this particular community.
This targeting raises serious concerns about the potential for the stolen data to be used maliciously, possibly for identity theft, hate crimes, or other forms of discrimination. It also underlines the importance of addressing not just the immediate cybersecurity implications but also the broader ethical considerations associated with targeted attacks on specific communities within the realm of genetic data.
23andMe responded promptly, confirming the incident and acknowledging that certain customer profile information was accessed without authorization. The company emphasized that there was no evidence of a breach within its own systems but rather the attackers utilized credentials leaked from other platforms to compromise accounts.
23andMe reiterated its commitment to user privacy and security, encouraging all users to enable multi-factor authentication (MFA) and avoid reusing passwords across different platforms.
As investigations into the breach continue, affected users are urged to take immediate steps to enhance their online security, such as enabling MFA and using strong, unique passwords.
Follow SecureWorld News for more stories related to cybersecurity.





