It's a damning report, and quite frankly, it is the last thing you want to hear about any company involved in the U.S. critical infrastructure.
NERC, which is the North American Electric Reliability Corporation, has just leveled a $10 million fine against an energy firm in the U.S. for violating 127 Critical Infrastructure Protection (CIP) standards. It says the violations put the bulk energy supply at risk:
"Many of the violations involved long durations, multiple instances of noncompliance and repeated failures to implement physical and cyber security protections."
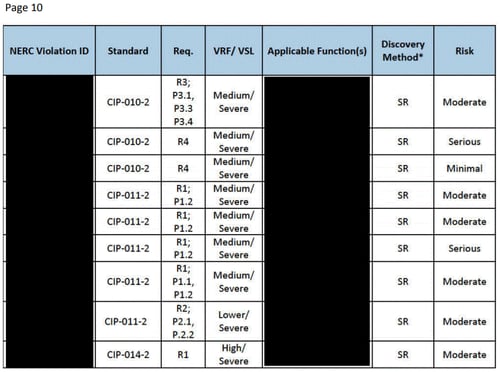
Heavily redacted report on violations
The list of security violations (just the violations) runs from pages 2-10. The details of the violations and the name of the company agreeing to pay the $10 million fine are redacted, although The Wall Street Journal is reporting that Duke Energy is the company listed somewhere among all these black boxes:
 4 organizational failures that led to security failures
4 organizational failures that led to security failures
Fortunately, the report highlights which types of failures led to such a major physical security and cybersecurity breakdown. Every organization, regardless of sector, can be on the lookout for these four contributing causes, cited in the report:
- "Lack of management engagement, support, and accountability related to the CIP (Critical Infrastructure Protection) compliance program"
- "Disassociation of compliance and security that resulted in a deficient program and program documents, lack of implementation, and ineffective oversight and training"
- "Organizational silos in the form of a lack of communication between management levels within the Companies, which contributed to a lack of awareness of the state of security and compliance"
- "Organizational silos across business units that resulted in confusion regarding expectations and ownership tasks, and poor asset and configuration management practices"
What is reasonable cybersecurity?
As our team read this report, it seemed to be the polar opposite of what cyber attorney Shawn Tuma told us about at a SecureWorld conference.
He shares what courts and counsel are looking for as "reasonable" cybersecurity, in this 90-second video:
3 reasons vendors might want to call Duke Energy
Required remediation efforts reveal general areas where the company was failing at physical security and cybersecurity, which is interesting to see if you're in InfoSec. And if you're a vendor, this list may be profitable, because the company has agreed to start:
- "Investing in enterprise-wide tools relating to asset and configuration management, visitor logging, access management, and configurations monitoring and vulnerability assessments"
- "Adding resources to help manage and implement compliance and security efforts"
- "Creating three levels of training (oversight training, awareness training for all staff, and performance training for staff implementing the security and compliance tasks)"
You can read the complete NERC Notice of Penalty for yourself for more details.
But you'll need some serious time because it is 250 pages long.
[RESOURCE: SecureWorld web conference, The Future of Securing Data Storage]




