What would you do if your finance manager wired $57,800 to a "trusted vendor," only to realize the email request was fraudulent?
In this digital world, business email compromise (BEC) is growing. BEC scams involving wire transfers increased by 33% in the second quarter of 2025. This illustrates how attackers are targeting financial workflows and payments.
Malware is no longer the basis for such attacks. They depend on trust.
With the growth of AI-generated messages, it's becoming difficult to differentiate between a legitimate message and a fraudulent one.
This article discusses seven tips to prevent business email compromise scams in 2026.
What is a BEC scam? 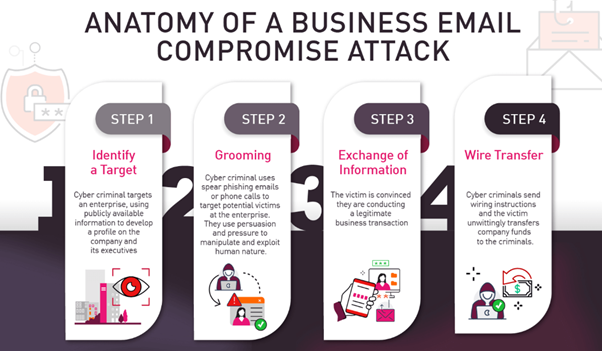
In a BEC scam, criminals use the identity of a partner, vendor, or executive. With this identity, they trick employees into sending sensitive information or money.
Consider that you are a CFO. You receive a fraudulent message that looks like a legitimate message from the CEO. The message asks for an urgent international wire transfer.
It was written in such a way that the tone sounds right. The signature matches. The timing feels believable. So, the transfer happens.
But it's a message that the CEO never sent.
BEC attacks use the power of urgency, authority, and familiarity. Their targets are finance teams, procurement departments, and HR—basically, anyone who handles payments or sensitive information.
In 2026, attackers will be able to send emails based on executive travel schedules, imitate writing styles, and replicate conversation threads using AI. They are extremely dangerous because of this.
The good news is that you can reduce your risk by implementing the right systems.
7 tips to prevent BEC scams in 2026
1. Enforce multi-factor authentication (MFA) across all accounts
If there's one control that immediately reduces risk, it's MFA. Even if attackers steal credentials through a phishing attack campaign, they still can't access an account without the second factor.
Don't limit MFA to executives. Apply it across:
-
Email accounts
-
Financial platforms
-
Cloud storage systems
-
Vendor portals
Use hardware keys or authentication apps rather than SMS when possible. The reason is that SMS-based MFA can be bypassed through SIM swapping.
Pro tip: Audit your MFA coverage quarterly. Many organizations think MFA is enabled, but it's not enforced on legacy accounts.
2. Implement SPF, DKIM, and DMARC email authentication
You can't prevent impersonation without technical controls.
SPF, DKIM, and DMARC work together to verify that emails actually come from authorized domains. Without them, attackers can spoof your domain and trick partners into trusting malicious messages.
Enabling strong email authentication reduces spoofing significantly. The email authentication methods, like DMARC, help protect users from impersonation at scale.
Set your DMARC policy to "reject," not just "monitor." Many businesses stop at the monitoring mode and never move forward.
Also, make it a point to:
-
Implement consistent DMARC monitoring to detect unauthorized domain usage
-
Review DMARC reports weekly
-
Remove unused domains
-
Lock down lookalike domains
Technical hygiene can prevent embarrassment and financial loss.
3. Establish a strict payment verification process
Here's where most companies fail: process discipline. No email alone should authorize a payment change.
Create a rule that any request involving money must be verified through a second channel. For example:
-
Call the vendor using a number already on file
-
Use secure vendor portals
-
Require two-person approval for large transfers
Many organizations also manage vendor communication and payment history through a cloud-based CRM, which helps finance teams verify requests using centralized records instead of relying only on email conversations.
Think about how many companies receive fake booking emails requesting updated bank details. Without a verification step, finance teams may process them without questioning.
Build friction into financial workflows. Convenience should never outweigh security.
Ask yourself: If a transfer request came in right now, how would your team verify it?
4. Train employees to recognize AI-powered social engineering
Technology alone won't save you. Employees must understand how modern scams look and feel. Today's attackers:
-
Mirror executive writing styles
-
Reference recent meetings
-
Use context pulled from LinkedIn
-
Create urgency with realistic deadlines
Today's attackers don't just copy writing styles—they also replicate branding details such as logos, formatting, and signatures. In some advanced cases, attackers even use an AI voice generator to create convincing audio messages that impersonate executives, adding another layer of urgency and realism to fraudulent payment requests.
Establishing internal standards for how to make an email signature ensures consistency across the organization, making it easier for employees to detect subtle differences in fraudulent messages.
Run scenario-based training sessions. Instead of boring slide decks, simulate real attacks. Send controlled internal tests and debrief afterward. It also helps to train employees on how legitimate financial communication should look, including standardized invoice email templates used by your organization. Send controlled internal tests and debrief afterward.
For example, an employee receives a message referencing a recent earnings call, asking for an urgent document review before market close. Would they question it?
Education builds instinct. And instinct stops mistakes.
Encourage a culture where employees feel safe reporting suspicious emails. Fear of embarrassment often prevents early reporting.
5. Monitor vendor and third-party email risks
Your organization might be secure, but have your vendors implemented security measures?
BEC attackers often compromise a supplier's mailbox and send legitimate-looking payment change requests from a real email thread.
This is particularly dangerous because:
-
The domain is authentic
-
The conversation history is real
-
The tone matches past communication
Imagine receiving a seemingly genuine invoice update from a travel partner. It looks just like previous correspondence, but it's malicious.
You've probably seen fake Robinhood email campaigns circulating online. Attackers exploit brand familiarity. The same principle applies to vendors.
You can mitigate this by:
-
Conducting vendor risk assessments annually
-
Limiting financial update privileges
-
Setting vendor-specific payment verification rules
Your defense is only as strong as your weakest partner.
6. Use AI-based email threat detection tools
If attackers use AI, so should you. Modern email security tools often analyze:
-
Behavioral anomalies
-
Writing tone deviations
-
Login location irregularities
-
Unusual financial language
For example, if your CEO never directly requests wire transfers but suddenly sends one, behavioral AI can flag the anomaly.
Layered protection works best with:
-
Secure email gateways
- Behavioral analytics
- Domain monitoring
- Real-time threat intelligence
Don't rely solely on traditional spam filters. BEC emails don't often contain malware or suspicious links; they look clean and legitimate. Your detection strategy must go beyond keyword scanning. In addition to enterprise-grade email security tools, endpoint protection solutions can provide an extra layer of defense by monitoring for malware and viruses, detecting data breaches, and enhancing device-level security.
While BEC attacks rely heavily on social engineering rather than malware, securing every endpoint reduces the overall attack surface and helps prevent credential theft that often fuels these scams.
7. Develop a rapid incident response plan
Even with strong defenses, assume that one of the attempts from the attackers succeeded.
What to do next? Every company needs:
-
A documented process to solve attacks
-
A 24-hour response protocol
-
Clear roles and responsibilities
-
Bank contact procedures
-
Legal and compliance notification steps
Time matters. The faster you contact financial institutions, the higher the chance of reversing transfers.
Run tabletop exercises twice a year. Walk through scenarios, such as a fraudulent transfer sent 45 minutes ago. What will your team do next to handle it?
Clarity reduces chaos, and preparedness reduces damage.
Build a resilient defense against BEC
BEC scams in 2026 are smarter, faster, and powered by AI. But implementing proper preventive measures can minimize the risk.
You can reduce your exposure through:
-
MFA
- Securing email authentication
- Verifying payments through secondary channels
- Training employees on modern social engineering
- Monitoring vendor risks
- Deploying AI-driven detection tools
- Maintaining a clear incident response plan
- Incorporating a reliable backup solution, like Office 365 email backup.
This isn't about adding complexity. It's about building discipline into how your organization communicates and moves money.
If you want to understand the evolving email threats and learn directly from cybersecurity leaders, explore upcoming events by SecureWorld. Practical insights from experts can strengthen your defense before the next attack happens.





.jpg)
