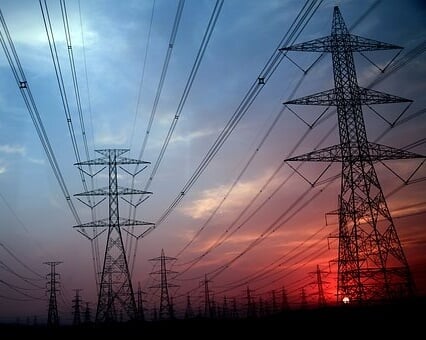
It is a dream scenario for hackers and terrorists. And a nightmare for the rest of us.
Cybercriminals could bring down the U.S. power grid, or power grids around the globe, without a cyber attack on the grid itself.
Instead, new research proves cybercriminals can attack the grid by controlling power-sucking devices we have connected to the web for our convenience.
Three Princeton researchers documented the frightening possibilities this week. Things like power line failures, voltage collapse, and persistent, wide-scale blackouts.
Power grid vulnerable to indirect cyber attack; how it works
The Internet of Things is fantastic.
Right?
You can tell your smart thermostat to kick on the air conditioning before you get home; you can warm up that shiny new IoT oven through an app on your phone; or you can activate your Wi-Fi enabled space heater without getting out of bed and walking across the room.
And these types of high voltage smart devices are exactly what hackers and cyber attackers can use to bring down the power grid.
Researchers call the blackout scenarios "MadIoT attacks," which stands for Manipulation of Demand via IoT.
And here's the thing. Your local electrical utility and the regional and national power grid operates like a well-oiled machine. Big data and analytics allow those in power generation and distribution to create accurate forecasts of how much power will be needed, where it will be needed, and when.
But according to Ivy League researchers Saleh Soltan, Prateek Mittal, and H. Vincent Poor, a sudden increase or decrease in power demand that is out of the "norm"
This control and the resulting rapid swing in power demand can trigger nightmarish power grid shut down scenarios that are hard to defend against and can be just as hard to reverse.
The big picture from power demand cyber attack study
The study includes a lot of technical details, but here is the big picture:
"... the normal operation of the power grid relies on the persistent balance between the supply and demand. Thus, an adversary’s approach could be to disrupt this balance using an IoT botnet. An adversary can leverage an IoT botnet of high-wattage devices and synchronously switch on all the compromised devices. If the resulting sudden increase in the demand is greater than a threshold... this consequently may result in the activation of the generators’ protective relays and loss of generators, and finally a blackout. Sudden decrease in the demand may also result in the same effect...."
- Line failure: As the system drops quickly out of balance, overloads in certain areas occur, shutting down certain lines.
- Cascading failure: After initial lines fail, that power has to go elsewhere in the system, which can result in additional overloads and line failures.
- Blackout: These failures may "eventually result in the separation of the system into smaller unbalanced islands and a large-scale blackout."
4 major problems if this power demand cyber attack occurs
The researchers also revealed four reasons this type of
- "The sources of the MadIoT attacks are very hard to detect and disconnect by the grid operator. The main reason is that the security breach is in the IoT devices, yet the attack is on the power grid."
- MadIoT attacks are easy to repeat. "Moreover, this repeatability allows an adversary to cause a persistent blackout in the power grid by disrupting the black start process...." (This is the process of bringing things back online after a blackout.)
- "The MadIoT attacks are 'black-box.' An adversary does not need to know the underlying topology or the detailed operational properties of the grid, albeit it can use the high-level information available on the ISOs’ websites to improve the timing of its attack." (ISO is an independent system operator.)
- "... power grids are not prepared to defend against the MadIoT attacks since abrupt changes in the demand are not part of the contingency list that grid operators are prepared for."
On that last point, the study clarifies that power operators and utilities have contingency plans to keep operating even if they lose their largest source of power generation. But all of these scenarios are "forecast" for, and a MadIoT botnet attack impacting power demand is not something electric companies plan for.
Researchers hope their study will change that.
And if it does not, we may someday think about their work in the darkness of a power outage.
[Note: Researchers presented a summary of their 32-page report, BlackIoT: IoT Botnet of High Wattage Devices Can Disrupt the Power Grid, at the USENIX Security Symposium, and based results on computer simulations using the same software that many in the power industry