The bomb threat email demands you pay $20,000 in Bitcoin or a bomb will go off.
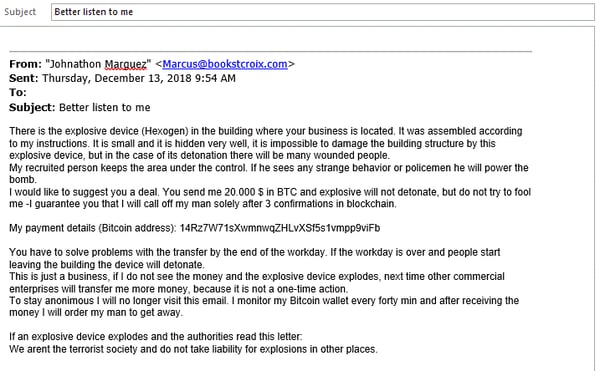
"There is the explosive device (Hexogen) in the building where your business is located. It was assembled according to my instructions. It is small and it is hidden very well, it is impossible to damage the building structure by this explosive device, but in the case of its detonation there will be many wounded people," the bomb extortion note reads.
And just like the Sextortion Email Scam in the fall of 2018, the bomb threat email now making the rounds includes a "do what I say or else" type of deadline:
"You have to solve problems with the transfer by the end of the workday. If the workday is over and people start leaving the building the device will detonate."
This was an interesting choice in wording. You have to solve the problems with the transfer probably refers to the fact that most people and most businesses have no idea how to make a payment in cryptocurrency.
Like anything else, doing it the for the first time can lead to problems you must overcome before really figuring it out. The cybercriminal is telling us to keep trying until we get it right.
Here is the actual bomb threat extortion email that appeared across the U.S. in a single day:
 Bomb threat email leads to panic, fear, anxiety across
Bomb threat email leads to panic, fear, anxiety across United States
Many Americans believed the bomb threat email could be legitimate. Bomb-sniffing dogs were called out, offices were evacuated, and there was confusion.
New York City Police officers searched for bombs:
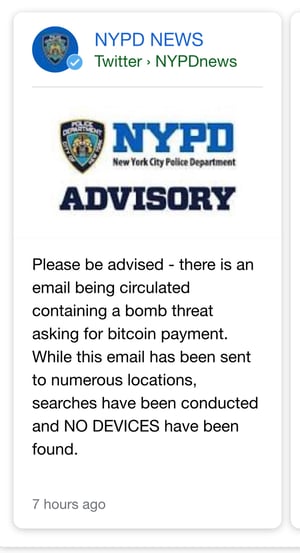 The bomb threat emails had people calling 9-1-1 in Denver:
The bomb threat emails had people calling 9-1-1 in Denver:

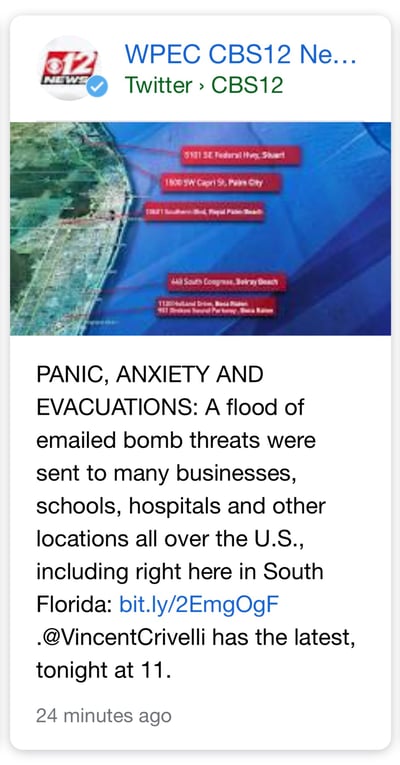
The bomb threat Bitcoin scam led to searches and fear in Florida:
 Police searched for bombs in the San Francisco Bay Area because of the bomb threat email:
Police searched for bombs in the San Francisco Bay Area because of the bomb threat email:
 We could go on. But this much is clear: the bomb extortion email created panic, anxiety, and evacuations in cities across the United States on December 13, 2018.
We could go on. But this much is clear: the bomb extortion email created panic, anxiety, and evacuations in cities across the United States on December 13, 2018.
Who sent the Bitcoin bomb threat emails?
This was most likely sent by a cybercriminal or a cybercrime group looking to make quick money. Some of the hottest email scams and ransomware cyber attacks have netted criminals millions in profits.
We recently interviewed hacking strategist J. Wolfgang Goerlich at SecureWorld about cybercrime trends he is seeing.
Cybercrime-as-a-service is growing
One of those trends is cybercrime-as-a-service, where one cybercriminal pays a hacker with a stolen database of emails (for example) to send out emails like the one we're talking about here.
Some hackers offer this as a subscription type service like paying for Netflix, but instead, this is for cybercrime and a chance to get rich:
"Criminal to criminal marketing as crimes of a service are on the rise. A lot these folks who are doing this are being sold the vision of, ‘oh, you can have a great life’ if you just buy our crime service and pay us a monthly fee. So... the sales of crime as a service will continue to rise."
Cigna CISO James Beeson tells SecureWorld that the spread of high-speed internet around the world combined with a low standard of living is helping to drive this cybercrime trend.
“If you’re making $10 a day and you can make more using Malware-as-a-Service, or a crime syndicate offers you $20 a day to help penetrate networks, what are you going to do?”
Cybersecurity and physical security are merging
We are sure this will increase the urgency of discussions about cybersecurity's impact on physical security at regional cybersecurity conferences in 2019.
No bombs, but how many people across the U.S. were told police could not help them because they were searching for bombs in offices or schools?
What if this type of cyber attack was merged with a real bomb or two? How would that have changed things?
Mukul Kumar, Chief Information Security Officer and VP of Cyber Practice at security vendor Cavirin,
And that is a problem.
“This demonstrates the need for organizations to conduct regular training of their employees as to the various threats," he says. As with any trend, there is a genuine product, and there are the copycats. This is obviously the latter.
However, given the availability of hacker tools for hire and personal data for rock-bottom prices, it will become harder to separate the two. The bad guys are looking for any vulnerabilities in one’s security controls. This is just another example, with the hope that a small percentage of the targets will act on the email.”
This time it was a bomb threat demanding Bitcoin. Who knows what it will be next time?
However, one thing is for sure: where there is money to make, cybercriminals will try to make it.




