The U.S. government solved the Equifax hack "whodunit" this week.
And it wasn't Colonel Mustard, in the kitchen, with the candlestick.
Instead, it was Chinese hackers, in 34 servers in 20 countries, with encryption.
Equifax data breach indictment: the suspects
Who are Wu Zhiyong, Wang Qian, Xu Ke, and Liu Lei?
According to newly unsealed U.S. court documents, these are the Chinese nationals responsible for the Equifax mega-breach. And they apparently hacked the company as part of an "economic espionage" plot with the backing of the Chinese government.
The U.S. Department of Justice (DOJ) released pictures of three of the four hackers:
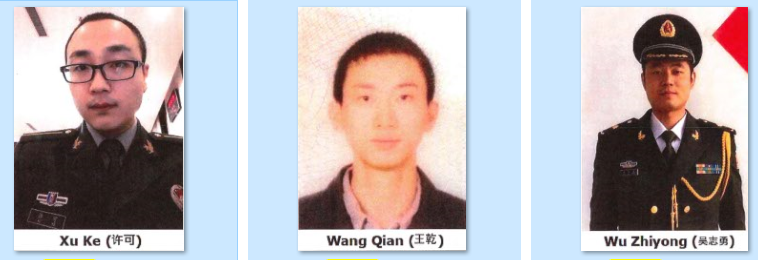
And according to the Equifax hacking documents reviewed by SecureWorld, the suspects are part of the Chinese military.
"Members of the People's Liberation Army (PLA), the armed forces of the People's Republic of China..."
Their photos support that idea. And we also learned that this gang of four pulled off the incredible from Shanghai, China:
"Accordingly, in a single breach, the PLA obtained sensitive personally identifiable information [PII] for nearly half of all American citizens."
They also stole data on nearly one million citizens of the U.K. and some 20,000 citizens of Canada.
Here is a look at how they committed the mega-breach that sent chills down the spine of cybersecurity professionals around the world.
Equifax breach indictment: 10 fast facts about hacker methods
The indictment in the Equifax hacking case is 24 pages long. Our SecureWorld editorial team just finished combing through it to develop this abbreviated list of key points.
1. Hackers exploited a cybersecurity hole
Using a security vulnerability that was known but remained unpatched at Equifax, hackers found a way in:
"The conspirators exploited the Apache Struts vulnerability to upload to an Equifax web server multiple unauthorized web shells and began reconnaissance on Equifax's online dispute portal." This included installing a "back door" to the system, so hackers could come and go as they pleased.
2. Hackers used that access to get to other databases.
"After gaining access to the web server, the conspirators interacted with Equifax's back-end databases by installing web shells created through Apache Struts and issue commands using Structure Query Language (SQL), a database management language commonly used to query and manipulate data."
3. Like many successful hackers, they kept poking and prodding, looking for more areas to explore and more treasures to find. How about some credentials?
"The conspirators also located and used Equifax database service credentials and thereby falsely represented that they were authorized users of Equifax's network, which permitted them to access additional back-end databases." By using these stolen credentials, they gained greater access and looked legitimate.
Equifax data breach indictment reveals what hackers did next
You could sum up this next section like this: query, compress, download, delete, and repeat.
4. The Equifax hackers had digital back doors propped open for access and some legitimate credentials to help with their investigation. Next, they conducted thousands of queries in a search for data to steal.
"In total, the attackers ran approximately 9,000 queries on Equifax's system while masking this activity through encrypted communication channels." And they found what they were looking for.
5. You can see why they used encryption:
"The majority of these queries were issued by conspirators using two China-based IP addresses that connected directly to Equifax's network."
6. Here comes another hacker best practice: If you find a massive data file you want to steal, take it out of the network in pieces.
"The conspirators stored the stolen information in temporary files, compressed and divided the large data files into more manageable file sizes for transmission, and executed HTTP commands to download the data files."
7. As they moved large amounts of data, the Equifax hackers took additional steps to hide the fact the data was destined for China.
"The conspirators attempted to hide the origin and location of their internet traffic and reduce the likelihood of detection by using approximately 34 servers located in nearly 20 countries to infiltrate Equifax's network."
8. Here are some other move-hiding techniques they used.
"The conspirators also employed a variety of encrypted login protocols, including Remote Desktop Protocol and Secure Shell Software, which permitted them to connect to servers over network connections from other servers they controlled."
9. They blended in with regular Equifax traffic.
"Additionally, the conspirators attempted to disguise their unauthorized access to Equifax's online dispute portal by using existing encrypted communication channels within Equifax's network to send questions and commands, which allowed them to blend in with normal network activity."
10. And the Equifax culprits performed another hacker best practice: cover your tracks.
"The conspirators deleted the compressed files after exfiltrating the sensitive data. In addition the conspirators configured settings on at least one of their leased servers that wiped log files on a daily basis in an effort to eliminate records of their activity."
U.S. Attorney General William Barr statement on Equifax indictment
In announcing the Equifax hacker charges, U.S. Attorney General William Barr underscored a message we have heard repeatedly: You cannot trust China.
"Today, we hold PLA hackers accountable for their criminal actions, and we remind the Chinese government that we have the capability to remove the Internet's cloak of anonymity and find the hackers that nation repeatedly deploys against us.
Unfortunately, the Equifax hack fits a disturbing and unacceptable pattern of state-sponsored computer intrusions and thefts by China and its citizens that have targeted personally identifiable information, trade secrets, and other confidential information."
Charges against the hackers include conspiracy to commit computer fraud, conspiracy to commit economic espionage, and conspiracy to commit wire fraud.
[RELATED: Can we trust Chinese tech giant Huawei? Listen to an interview with the CSO of Huawei USA on The SecureWorld Sessions podcast.]
All four hackers in the case are believed to be in China and out of reach of U.S. law enforcement.
But FBI Deputy Director David Bowdich says the government's work here is not done:
"This is not the end of our investigation; to all who seek to disrupt the safety, security and confidence of the global citizenry in this digitally connected world, this is a day of reckoning.”
We'll see if that turns out to be true.
RELATED: The United States vs. Equifax Hackers, Indictment (PDF)
RESOURCE: SecureWorld cybersecurity conferences across North America




