It's almost impossible to keep up with the number of news items that come out daily about new or emerging ransomware or cyber threats or respectable companies that had eye-opening breaches.
Here's a few from this week that are worth taking note of.
Deadbolt ransomware variant
This summer has seen an increase in attackers' use of the Deadbolt ransomware variant, which affects network-attached storage (NAS) devices. The U.S. is most affected, with Germany and Italy following suit with registered attacks. This article does a good job of updating the variant that targets devices made my Taiwanese company QNAP. This report dives into how this growing tactic works, including how NAS boxes are vulnerable due to their "plug-and-play" nature for network attached storage. Here's an article we ran in February about a Deadbolt decryption key being released.
Cisco reports stolen data
An intrusion in May resulted in data being stolen from Cisco Systems and then placed on the Dark Web. A personal Google account was the culprit, according to Cisco Security Incident Response. To blame? The Yanluowang ransomware gang. When Cisco refused to pay the ransom, the bad actors posted the stolen data, claiming there were thousands of files totaling 55 GB from a cache. Here's one report of the incident. The Yanluowang group is linked to "Evil Corp," the Lapsus$ gang (responsible for a recent Uber attack), and FiveHands malware.
Google Play and Apple Store caught in adware scheme
Google Play and Apple's App Store are reeling from security researchers identifying 13 million app installations linked to 75 fraudulent ads tied to adware on Google Play and another 10 on Apple's App Store. The new ad fraud campaign is named "Scylla" and is the continuation of a malicious campaign that started in 2019. See the list of the most downloaded adware apps.
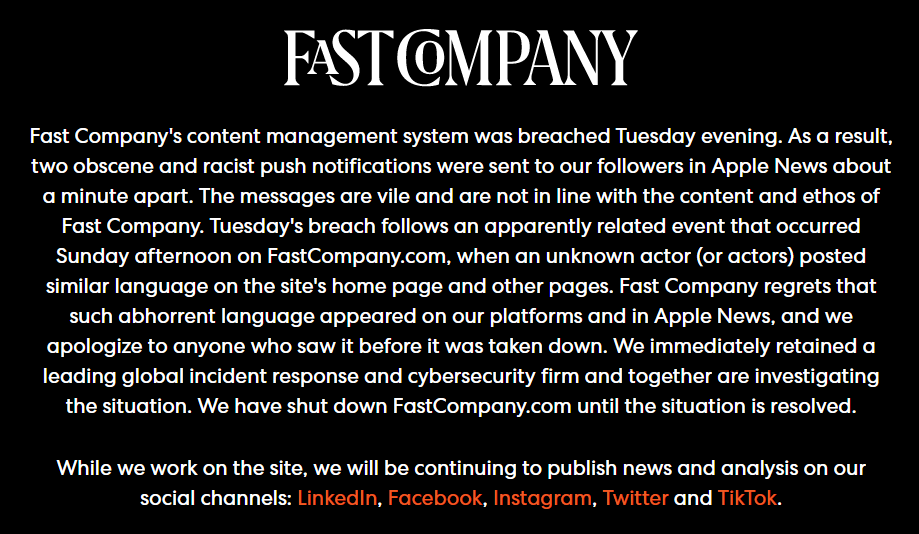
Hackers breach 'Fast Company' systems
Fast Company, known for staying ahead of the tech and innovation game with its business news publication, was hacked this week and offensive push notifications were sent out to Fast Company users, specifically through Apple News. The breach followed a separate attack to FastCompany.com over the weekend, which led to similar unpleasant language being shared on the site's homepage and other website pages. Here's TechCrunch coverage, as well as Fast Company's statement:
Bleeping Computer reports that hackers working for Russia are using mouse movements in Microsoft PowerPoint presentations to garner access and trigger malicious scripts. APT28, or "Fancy Bear," is the threat group responsible for deploying the technique for delivering the Graphite malware. Two slides in a PPT file wrongly credited to come from an international organization working toward improving the economy and trade worldwide feature instructions for the Interpretation option in Zoom video conferencing app.
Coreid, the ransomware-as-a-service group behind the Noberus ransomware, continues to sophisticate its ransomware and affiliate programs in efforts to steal data and credentials from compromised networks. Since around 2012, Coreid and its implementers are known for using the Carbanak malware to steal money from mainly the banking, hospitality, and retail industries. This article has more.
The good of AirTags being exploited for bad
News has been reported since early 2021 about Apple AirTags—little devices attached to keys, luggage, computer bags, or any personal belonging so iPhone users can find their stuff when they or someone else has misplaced it. Ripe for exploitation, hackers have figured out how to clone these devices and, essentially, throw the AirTag user off the trail. Not surprisingly, some creeps are using the devices to slip into people's belongings so they can track where they work or live. Here's what Apple has to say about it:
"We also have seen reports of bad actors attempting to misuse AirTag for malicious or criminal purposes. Apple has been working closely with various safety groups and law enforcement agencies. Through our own evaluations and these discussions, we have identified even more ways we can update AirTag safety warnings and help guard against further unwanted tracking."





