It is the digital version of the Trojan horse.
The software updates for your IT management tools arrive automatically and contain legitimate changes—but hidden inside the update is malware that gives hackers secret access to your network.
In modern times, this is called a supply chain cyberattack. And according to the U.S. government and prominent security researchers, this type of attack is playing out right now on a global scale.
IT monitoring software company victim of supply chain cyber attack
More than 300,000 organizations and governments around the world rely on a company called SolarWinds. It makes software to help monitor and manage IT systems.
And in this rapidly developing cyberattack, high value SolarWinds customers are currently being attacked through this digital Trojan horse type of cyberattack.
The United States government even appears to be one of the victims.
How urgent is this cyber situation? Urgent enough that the Cybersecurity and Infrastructure Security Agency (CISA) issued a rare weekend alert about the attack and so did researchers at FireEye along with SolarWinds itself.
"SolarWinds has just been made aware our systems experienced a highly sophisticated, manual supply chain attack on SolarWinds® Orion® Platform software builds for versions 2019.4 HF 5 through 2020.2.1, released between March 2020 and June 2020.
We have been advised this attack was likely conducted by an outside nation state and intended to be a narrow, extremely targeted, and manually executed attack, as opposed to a broad, system-wide attack. We recommend taking the following steps related to your use of the SolarWinds Orion Platform."
If you are a SolarWinds customer, we'll talk about mitigation techniques in a moment. First, however, let's take a look at how the SolarWinds back door attack works. Security researchers say there are ways to detect the attack but only if you know what to look for and are actively looking for those things.
SolarWinds supply chain attack ongoing: how it works
FireEye researchers say this is an ongoing cyberattack and that nation-state hackers are most likely behind the attack because of its sophistication.
"This is some of the best operational security that FireEye has observed in a cyber attack, focusing on evasion and leveraging inherent trust."
Think about that statement for a moment.
FireEye researchers report regularly on the world's most prominent cyberattacks. In some ways, they've seen it all. And this attack was carried out with operational elegance.
So how does it work? Researchers break it down into these basic stages.
1. The supply chain attack trojanizes the SolarWinds Orion business software updates in order to distribute a new malware it is calling SUNBURST. This malware arrives with a legitimately signed certificate.
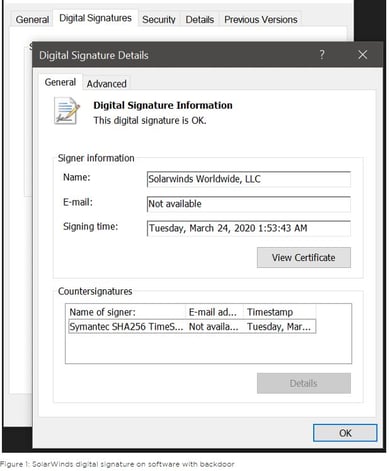
"The trojanized update file is a standard Windows Installer Patch file that includes compressed resources associated with the update, including the trojanized SolarWinds.Orion.Core.BusinessLayer.dll component."
2. After SUNBURST malware is dropped into the network via the SolarWinds update, the malware sits silently before springing to life:
"After an initial dormant period of up to two weeks, it retrieves and executes commands, called 'Jobs,' that include the ability to transfer files, execute files, profile the system, reboot the machine, and disable system services.
The malware masquerades its network traffic as the Orion Improvement Program (OIP) protocol and stores reconnaissance results within legitimate plugin configuration files allowing it to blend in with legitimate SolarWinds activity. The backdoor uses multiple obfuscated blocklists to identify forensic and anti-virus tools running as processes, services, and drivers."
And FireEye has taken a close look at the code involved in the attack:
"We are currently tracking the software supply chain compromise and related post intrusion activity as UNC2452. After gaining initial access, this group uses a variety of techniques to disguise their operations while they move laterally. This actor prefers to maintain a light malware footprint, instead preferring legitimate credentials and remote access for access into a victim’s environment."
This includes command and control traffic that masquerades as the legitimate Orion Improvement Program and code that hides in plain sight by using fake variable names and tying into legitimate components.
And speaking of hiding in plain sight, the malware in this attack does that in several other ways, as well, according to researchers:
"The attacker used a temporary file replacement technique to remotely execute utilities: they replaced a legitimate utility with theirs, executed their payload, and then restored the legitimate original file. They similarly manipulated scheduled tasks by updating an existing legitimate task to execute their tools and then returning the scheduled task to its original configuration. They routinely removed their tools, including removing backdoors once legitimate remote access was achieved."
And now the attackers are able to blend in to more easily move around and find the data they are looking to access.
U.S. government a victim of the SolarWinds supply chain cyberattack
So which organizations and which governments are known victims of the SolarWinds supply chain attack?
For one thing, we know that SolarWinds is an attack victim itself. And for another, we know it has clients around the globe that are becoming victims:
"FireEye has detected this activity at multiple entities worldwide. The victims have included government, consulting, technology, telecom and extractive entities in North America, Europe, Asia and the Middle East. We anticipate there are additional victims in other countries and verticals. FireEye has notified all entities we are aware of being affected."
And if reporting by the Washington Post is correct, this attack is most likely being committed by Russian nation-state hackers who successfully infiltrated the U.S. Treasury Department and a part of the U.S. Department of Commerce, among other high-value targets:
"All of the organizations were breached through a network management system called SolarWinds, according to three people familiar with the matter, who spoke on condition of anonymity because of the issue's sensitivity."
That Washington Post story appeared hours before the FireEye alert and the SolarWinds Security Advisory.
SecureWorld News reached out to the U.S. Department of Commerce and a spokesperson for the department verified that there is a breach investigation underway:
"We can confirm there has been a breach in one of our bureaus. We have asked CISA and the FBI to investigate, and we cannot comment further at this time."
And the initial results of that investigation have the U.S. government ordering agencies to shut off instances of SolarWinds immediately, no later than noon ET on December 14, 2020. This is detailed in Emergency Directive 21-01.
If you read our story on the recent data breach and theft of FireEye Red Team tools, you may wonder if that theft had anything to do with the ability to launch the supply chain attack.
Brandon Hoffman, Chief Information Security Officer at security firm Netenrich, doubts this is the case:
"It's natural to think that just after the FireEye breach, adversaries turned their tools to use and perpetrated this breach of the Commerce department. However, careful examination of this seems to lead us to the conclusion that this has been going on much longer.
The type of attack described to date involves several low and slow techniques. The very term advanced persistent threat (APT) was coined to describe an attack just like this."
How can SolarWinds customers mitigate the supply chain attack?
SolarWinds says it already is offering customers a "hotfix" release that will end the malware delivery, and another update is coming out this week that both replaces the compromised component and provides several additional security enhancements.
In the meantime, SolarWinds says organizations should take these steps:
"The primary mitigation steps include having your Orion Platform installed behind firewalls, disabling internet access for the Orion Platform, and limiting the ports and connections to only what is necessary."
Also, FireEye detailed MITRE ATT&CK techniques observed and all kinds of technical details to hunt for on your network which could be indicators an attack is happening to your organization. Plus, it included countermeasures you can employ.
Deep Dive: FireEye Github page on SolarWinds attack and SUNBURST malware
In the meantime, let this story be a reminder that supply chain attacks are real and remain a threat to organizations and governments.