Iran's cyber warfare operations are not typically covered as extensively as some others.
However, Iran is considered one of the major cyber threats to U.S. critical infrastructure and organizations.
What makes Iran's military hacking methods a significant threat?
Colonel Cedric Leighton, a CNN military analyst and former Air Force Colonel, explains the reasons to SecureWorld:
"Iran, of course, is a key player. Their cyber methods include such things as malware insertions, such as MUD-ing, wiper attacks, like the Shamoon virus.
Phishing is used by the Iranians, as well as distributed-denial-of-service [DDoS] attacks, for example, against the banking industry, some ransomware, and also, to some extent, disinformation campaigns that they mount within cyberspace, using everything from Twitter to other social media platforms, both pertaining to Iranian interests, as well as allied interests via Iran, such as Hamas."
SecureWorld News researched Iran-backed hackers currently on the FBI's Most Wanted list. And these hackers are still at large today.
Iranian threat actors: What are the motives behind the attacks?
FBI Director Christopher Wray testified before U.S. Congress in September on why Iran continues to be a threat in terms of terrorist operations in the physical world.
Tensions were heightened when Islamic Revolutionary Guard Corps-Qods Force (IRGC-QF) Commander Qassem Soleimani was assassinated in January 2020.
"Iran and its global proxies and partners, including Iraqi Shia militant groups, continue to attack and plot against the United States and our allies throughout the Middle East in response to U.S. pressure. Iran's Islamic Revolutionary Guard Corps-Qods Force continues to provide support to militant resistance groups and terrorist organizations. Lebanese Hizballah, Iran's primary strategic partner, has sent operatives to build terrorist infrastructures worldwide.
Hizballah also continues to conduct intelligence collection, financial activities, and procurement efforts worldwide to support its terrorist capabilities."
In the digital world, bad actors are using social engineering methods to hack on behalf of the Iranian government, even threatening the 2020 U.S. election process.
"Iran used cyber means to try to sow divisions and undermine our elections, targeting voters before the November election, and threatening election officials after," Wray said.
Col. Leighton also says Iran's motives fall into several categories: geopolitical, religious, and economic.
"They [Iran's government] want to make sure that no one either at home in Iran or overseas who has any interest in Iranian politics can do anything to remove the current religious government. And they have economic reasons in the sense that they also want to circumvent very tight and very crippling sanctions that have been levied against Iran for many, many years."
And this face-off continues:
"The U.S. and Israel are top targets due to their longstanding adversarial relationships with the current Iranian government dating back to their support for the former Iranian monarchy and persisting into the present day with their efforts against Iran's nuclear program," Paul Prudhomme, Head of Threat Intelligence Advisory for IntSights, told The Daily Swig.
In recent news, there have also been gas station cyberattacks, which Iran is claiming were carried out by the U.S. and Israel.
The evolution of Iran's cybercrime objectives
Though the cyberattacks orchestrated by Iran's government are not widely considered as sophisticated or advanced as those carried out by Russia or China, the techniques have grown over the years. Traditionally, these attacks put an emphasis on social engineering, finding innovative new ways to defraud end-users.
This does not mean actors are not actively seeking to up their technological impact, including aggressively pursuing ransomware methods.
Emiel Haeghebaert, Associate Analyst for Mandiant Threat Intelligence, told The Daily Swig:
"Iranian cyber operations started as low-level defacements often conducted by the 'Iranian Cyber Army.' As the government and military cyber programs matured, however, we started observing more advanced activity in line with Iran's strategic priorities…
We believe that Iran started heavily investing in its cyber operations program following the discovery of Stuxnet in 2010, and we can track the evolution from there.
Simultaneously, however, we have seen some indication that Iran is conducting more aggressive operations designed to disrupt their target's networks and day-to-day operations, including through ransomware."
In a Forbes article, a former military colonel for British intelligence named Philip Ingram made no qualms about Iran's cyberwarfare tactics, even commenting that Iran has "first world cyberattack capability."
"Iran has a very sophisticated broad spectrum of capabilities able to target critical national infrastructure, financial institutions, education establishments, manufacturers and more," Ingram said.
As you will see from this list, these hackers have infiltrated systems and left a path of destruction behind them.
The FBI's most wanted Iran-backed hackers
1. IRGC-affiliated cyber actors go after U.S. government agents
-png.png)
Proving you never know who you can trust, a former U.S. Air Force intelligence specialist named Monica Elfriede Witt banded up with other malicious hackers to run an espionage campaign against U.S. intelligence personnel in 2019.
"Once a holder of a top secret security clearance, Monica Witt actively sought opportunities to undermine the United States and support the government of Iran—a country which poses a serious threat to our national security," said Executive Assistant Director Jay Tabb of the FBI's National Security Branch at a press briefing.
Charges come against Mojtaba Masoumpour, Behzad Mesri, Hossein Parvar, and Mohamad Paryar for the roles they played in threatening national security.
"The Iranian cyber conspirators conspired to commit computer intrusions targeting certain United States Government Agents, using malicious code, fictitious and imposter online personas and accounts, and information gathered about the victims to gain unauthorized access to protected computers and computer networks," reads a statement by the FBI.
All five of the suspects are still believed to be in Iran.
2. The MABNA hackers

This APT group, commonly called The MABNA Institute, were indicted by the U.S. District Court for the Southern District of New York in 2018.
"Nine Iranian citizens working at the behest of the government of Iran have been indicted in a computer hacking campaign that compromised universities, private companies, and government entities," reads a statement by the FBI.
"As alleged in the indictment, the men were involved in a scheme to obtain unauthorized access to computer systems, steal proprietary data from those systems, and sell that stolen data to Iranian customers, including the Iranian government and Iranian universities. Each individual was a leader, contractor, associate, hacker for hire, or affiliate of the Mabna Institute, a private government contractor based in the Islamic Republic of Iran that performed this work for the Iranian government, at the behest of the Islamic Revolutionary Guard Corps."
In their work, these men—Gholamreza Rafatnejad, Ehsan Mohammadi, Seyed Ali Mirkarimi, Abdollah Karima, Mostafa Sadeghi, Sajjad Tahmasebi, Mohammed Reza Sabahi, Roozbeh Sabahi, and Abuzar Gohari Moqadam—primarily targeted universities.
In total, victims of their attacks reached more than 300 educational institutions worldwide in more than 20 countries, including the U.S. This group also attacked five federal and state agencies in the U.S. and more than 36 private companies in the U.S. and abroad.
Research conducted by Recorded Future made some interesting discoveries about MABNA Institute, too.
"Notably, our research did not reveal new evidence of the threat actor's adoption of malware in its campaigns. This continues to suggest that while the threat actor is highly determined to lead its credential theft operations internationally and sell credentials inside Iran to research-oriented organizations, it likely sees no practical use to maintaining persistence in victim networks."
3. IRGC aerospace and satellite espionage cyber actors
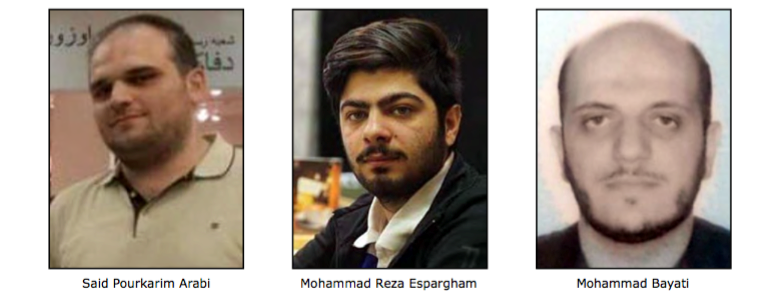
Criminal charges have been announced against these hackers with ties to the IRGC and an intention to disrupt the U.S. aerospace and satellite sectors.
Said Pourkarim Arabi, Mohammad Reza Espargham, and Mohammad Bayati used social engineering strategies in a coordinated attack to steal the identities of U.S. citizens and access critical information related to the technology used.
Just some of the other tactics used by these bad actors included vandalism of websites under the name "Sejeal" and intellectual property theft.
The campaign by these nation-state hackers started back in 2015 and included a hit list of more than 1,800 accounts from organizations in five countries, including the U.S., Australia, Israel, Singapore, and the United Kingdom.
According to a release by the FBI, this group was more technologically savvy, and used eight different malware varieties under the guise of a shell company called Rana Intelligence Computing Company to gain access to sensitive information. Rana currently has sanctions imposed against it by the U.S. Department of the Treasury.
4. The DDoS nation-state hackers
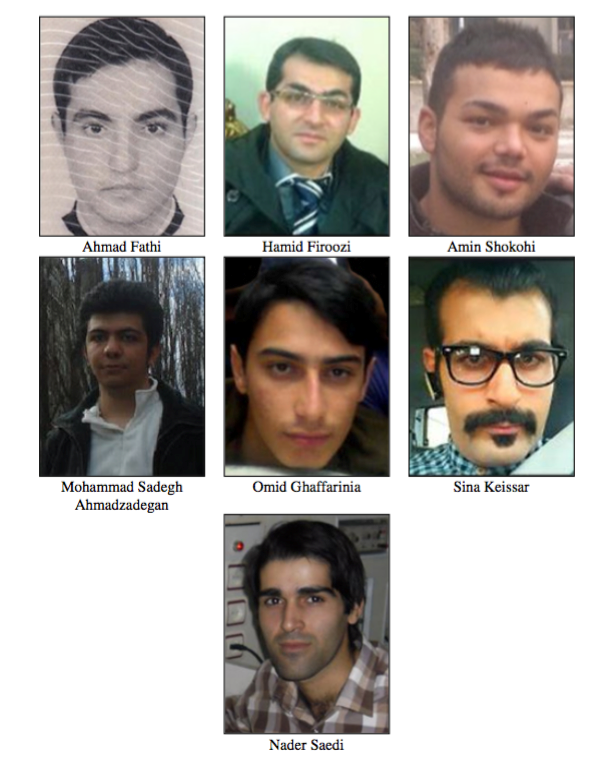
These men perpetrated distributed-denial-of-service (DDoS) attacks in a coordinated effort to cause disruption in American financial institutions.
"Each defendant was a manager or employee of ITSecTeam or Mersad, private security computer companies based in the Islamic Republic of Iran that performed work on behalf of the Iranian Government, including the Islamic Revolutionary Guard Corps," said an FBI statement.
In 2016, a grand jury representing the Southern District of New York indicted the Iranian nationals Sina Keissar, Ahmad Fathi, Hamid Firoozi, Amin Shokohi, Mohammad Sadegh Ahmadzadegan, Omid Ghaffarinia, and Nader Saedi.
According to a New York City federal court, the attack campaign is believed to have started around late 2011 and ramped up quickly.
"The DDoS campaign began in approximately December 2011, and the attacks occurred only sporadically until September 2012, at which point they escalated in frequency to a near-weekly basis, between Tuesday and Thursdays during normal business hours in the United States. On certain days during the campaign, victim computer servers were hit with as much as 140 gigabits of data per second and hundreds of thousands of customers were cut off from online access to their bank accounts," the Department of Justice (DOJ) said in a release.
Four of the seven men also managed a botnet for cyberattack purposes.
In one of the worst incidents, which took place between August and September 2013, one member gained authorization to break into the Bowman Dam's protected computer, which could have impacted New York City's water supply.
The FBI is currently working to bring these hackers to justice. If you have any information relevant to these cases, report it to the FBI or an American embassy or consulate. You can also submit an anonymous tip online.
[RESOURCE] Data are everywhere, but do you know where the most critical data are in your organization? Catch the webcast, It's 2 AM. Do You Know Where Your Data Is?, to learn more about security and compliance-related matters. Earn CPE credit for your attendance.




