The controversial Pegasus spyware continues to stay in the news cycle, as a new report from the Citizen Lab details how the technology was used to target pro-democracy activists in Thailand.
Thailand is currently in the midst of some political upheaval (who isn't?) after its 2019 elections—its first elections since a military coup in 2014—failed to restore parliamentary democracy and returned the coup leaders to power.
Understandably, this led to mass protests and social media campaigns like #WhyDoWeNeedAKing and #FreeYouth. The current Thai government was not exactly thrilled by this and responded with a wave of arrests and increased surveillance dramatically. The Citizen Lab sums up the situation in one sentence:
"National legislation in Thailand has thus far failed to introduce checks and balances against the government's broad and continuously evolving surveillance powers, while mechanisms to hold the government accountable are being weakened and attacks against civil society continue."
The increase in surveillance also means the use of Pegasus spyware.
Pegasus spyware in Thailand
If you are not familiar, Pegasus is the flagship product sold by the Israel-based NSO Group. The company claims it is only sold to vetted government agencies for the purpose of spying on criminal and terrorist activity, but there is a trove of evidence that suggests the spyware is used for much more than that.
Pegasus has been used to target journalists at Al Jeezera, Senior EU officials, the Prime Minister of Spain, and so many more individuals around the world ranging from activists, politicians, and business leaders.
The spyware has also been blacklisted by the United States government and is currently dealing with a lawsuit from Apple stemming from its alleged ability to hack iPhones using previously undiscovered Zero-Day vulnerabilities.
So, what is the situation in Thailand?
In 2018, the Citizen Lab reported on a potential Pegasus operator being located within the country. A couple years later in November 2021, Apple began sending notifications to users who were targeted with mercenary spyware. Many recipients of this notification contacted the Citizen Lab, which then launched an investigation. Here are some of its findings:
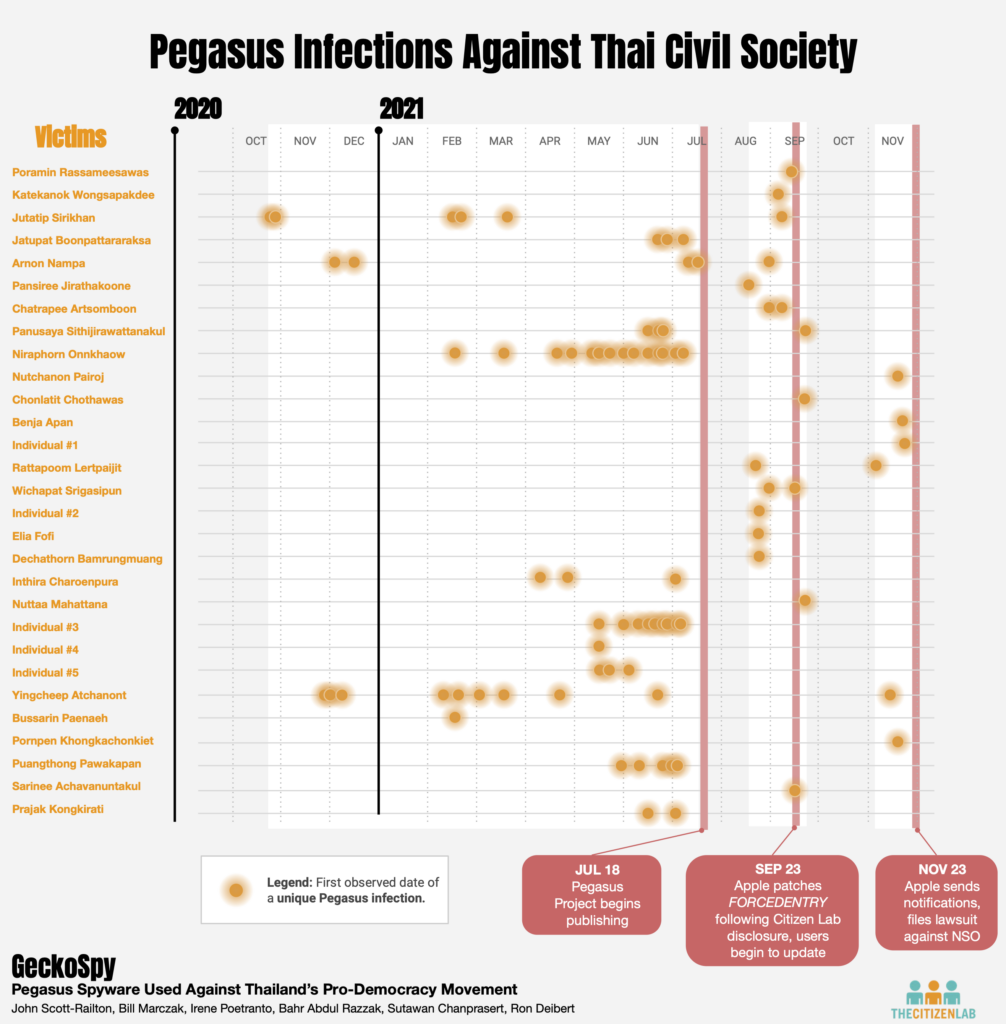
"We have identified at least 30 Pegasus victims among key civil society groups in Thailand, including activists, academics, lawyers, and NGO workers. The infections occurred from October 2020 to November 2021, coinciding with a period of widespread pro-democracy protests, and predominantly targeted key figures in the pro-democracy movement. In numerous cases, multiple members of movements or organizations were infected.
Many of the victims included in this report have been repeatedly detained, arrested, and imprisoned for their political activities or criticism of the government. Many of the victims have also been the subject of lèse-majesté prosecutions by the Thai government."
The lèse-majesté law criminalizes defamation, insults, and threats to the Thai royal family.
The chart below details the uncovered Pegasus infections:
The Citizen Lab notes in the report that the forensic evidence collected from the infected devices does not provide conclusive evidence that a single NSO customer was behind these attacks. But when looking at all the other facts of the case, it certainly suggests at least one Pegasus operator in Thailand is responsible. Specifically, the Citizen Lab notes these four observations:
- "The victims were of intense interest to the Thai government."
- "The hacking points to a sophisticated understanding of non-public elements of the Thai activist community, including funding and roles of specific individuals."
- "The timing of the infections is highly relevant to specific political events in Thailand, as well as specific actions by the Thai justice system. In many cases, for example, infections occurred slightly before protests and other political activities by the victims."
- "There is longstanding evidence showing Pegasus presence in Thailand, indicating that the government would likely have had access to Pegasus during the period in question."
For more information on Pegasus spyware in Thailand, check out the full report from the Citizen Lab.





