Livestreaming platform Twitch, frequented by a community of online gamers, experienced a massive data breach.
Initially, the responsible actor appears to have released gamer incomes from the service, but the hacker has already threatened more is to come.
And at least some of the information appears to be about Twitch's security team.
Twitch confirmed a breach had happened through a tweet:
We can confirm a breach has taken place. Our teams are working with urgency to understand the extent of this. We will update the community as soon as additional information is available. Thank you for bearing with us.
— Twitch (@Twitch) October 6, 2021
Here's what we know now about the incident.
How did the Twitch cyber incident go down?
Early Wednesday morning, a hacker posted to online forum 4chan bragging about their actions. The first post was titled "part one," which indicates there could be more problematic leaks later on.
The original post by the perpetrator can be seen below. A motivator behind the attack appears to be the Twitch gaming culture and Twitch's new partnership with Amazon Game Studios.
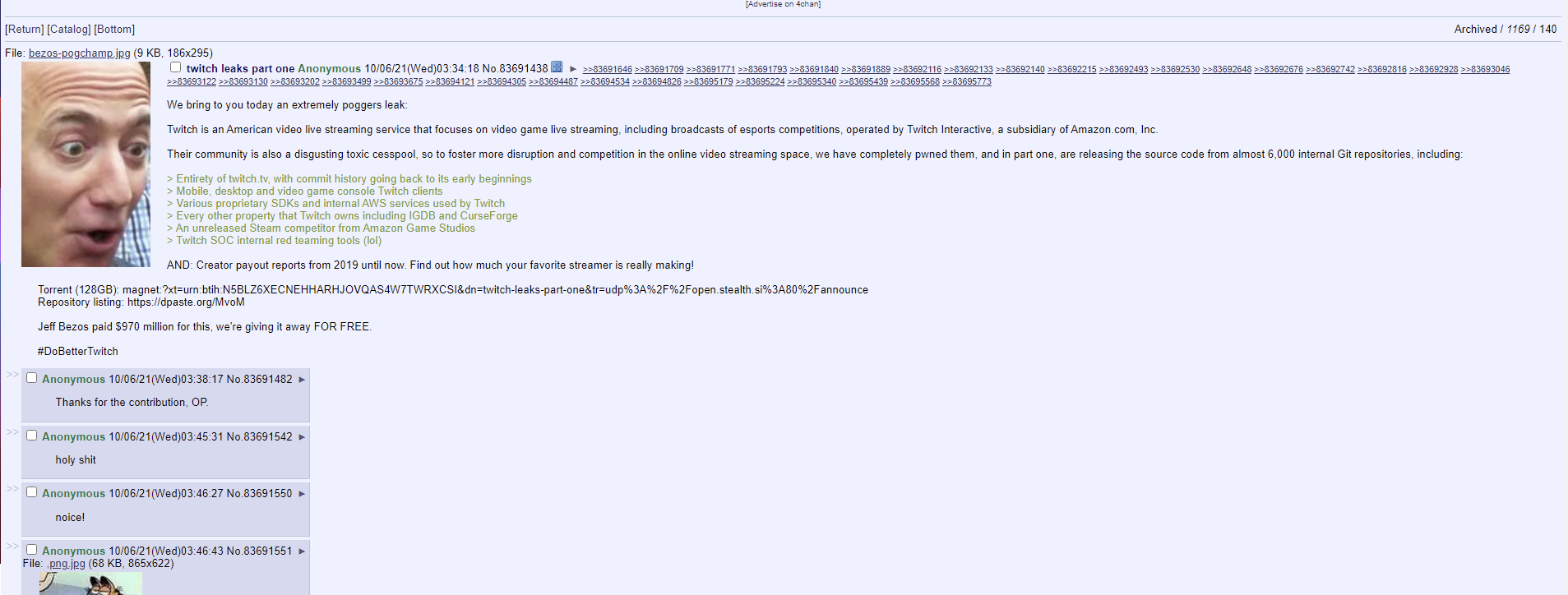
According to a separate post, the likely entryway for the hacker was through a GitHub internal repository, where they could then access a 128Gb torrent containing the data.
James Chappell, Co-Founder and Chef Innovation Officer of Digital Shadows, discussed how the actor accessed this information. He said:
"There appears to be evidence that the original files came from an internal GitHub server, git-aws.internal.justin.tv, was at least part of the breach. Justin.tv was the name of a company that eventually transformed into Twitch. It rebranded as twitch in 2011, so this looks like a long-standing piece of infrastructure."
From that point of view, what else could the hacker release and will this leak be detrimental for Twitch users?
To date, there have been no reports that username and password information was leaked. However, that does not mean it has not been accessed.
"Whilst user data does not currently appear to be in the archive, users on the forum are speculating as to what may follow," Chappell said.
Response to the initial incident and #DoTwitchBetter campaign
The initial leak focused on the profit that streamers make on the platform, which according to PC Gamer is not surprising information or even difficult data to get one's hands on.
Chappell continued that some streamers might be concerned by the incident, since it reveals their incomes from the service.
"We know that streamers will be concerned about the impact of their streaming revenues being made public given that they rely on donations from fans. The Twitch security team's details have been leaked alongside this first dump. Currently users on 4chan seem to be crowdsourcing the analysis of what appears in this dump, so expect more details to drop throughout the day," he said.
While this is a substantial data leak, the majority of influencer-level streamers known for using the platform seemed unfazed or unsurprised at the very least. One gamer, negaoryx, shared her response on Twitter.
streamers who moved to YouTube seeing the Twitch leak pic.twitter.com/Hg5EbAArDN
— negaoryx (@negaoryx) October 6, 2021
Other users were eager to help fellow gamers, stating the unencrypted stream keys could cause disruption.
Twitch streamers:
— Rhiebelle (He/She/They) (@rhiebelle) October 6, 2021
Off the back of the breach our stream keys have also been leaked unencrypted.
Go to your dashboard and reset your stream key to keep your streams safe going forward. 💙 pic.twitter.com/CMgOKY2MQo
Twitch has also been at the center of controversy, which some are claiming created an uncomfortable and unsafe environment online.
About two months ago, Twitch released a statement saying the company had been working on the problem.
"We've seen a lot of conversation about botting, hate raids, and other forms of harassment targeting marginalized creators. You're asking us to do better, and we know we need to do more to address these issues," Twitch wrote on Twitter.
Based on the hacker's 4chan posts, the campaign for Twitch to "do better" could be part of the hacker's motivation, as well.
It's still yet to be seen if this breach will lead to more sensitive information being leaked. SecureWorld News will update this story as more information becomes available.
[RESOURCE] In cybersecurity, it is necessary to stay one step ahead at all times. In partnership with promoting Cybersecurity Awareness Month, register to join the Remote Sessions webcast, Always Aware: Continuing Your Cybersecurity Awareness Month Journey. Attendance is eligible for CPE credit.