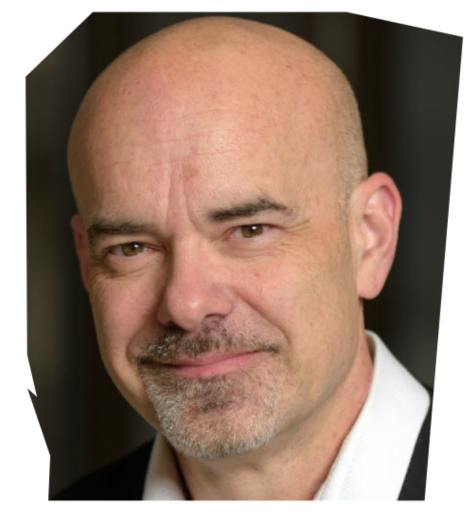
Dr. Larry Ponemon is the Chairman and Founder of the Ponemon Institute, a research “think tank” dedicated to advancing privacy and data protection practices. Dr. Ponemon is considered a pioneer in privacy auditing and the Responsible Information Management or RIM framework.
Ponemon Institute conducts independent research, educates leaders from the private and public sectors and verifies the privacy and data protection practices of organizations in a various industries. In addition to Institute activities, Dr. Ponemon is an adjunct professor for ethics and privacy at Carnegie Mellon University’s CIO Institute. He is a Fellow of the Center for Government Innovation of the Unisys Corporation.
Dr. Ponemon consults with leading multinational organizations on global privacy management programs. He has extensive knowledge of regulatory frameworks for managing privacy and data security including financial services, health care, pharmaceutical, telecom and Internet. Dr. Ponemon was appointed to the Advisory Committee for Online Access & Security for the United States Federal Trade Commission. He was appointed by the White House to the Data Privacy and Integrity Advisory Committee for the Department of Homeland Security. Dr. Ponemon was also an appointed to two California State task forces on privacy and data security laws.
Dr. Ponemon earned his Ph.D. at Union College in Schenectady, New York. He has a Master’s degree from Harvard University, Cambridge, Massachusetts, and attended the doctoral program in system sciences at Carnegie Mellon University, Pittsburgh, Pennsylvania. Dr. Ponemon earned his Bachelors with Highest Distinction from the University of Arizona, Tucson, Arizona. He is a Certified Public Accountant and a Certified Information Privacy Professional.